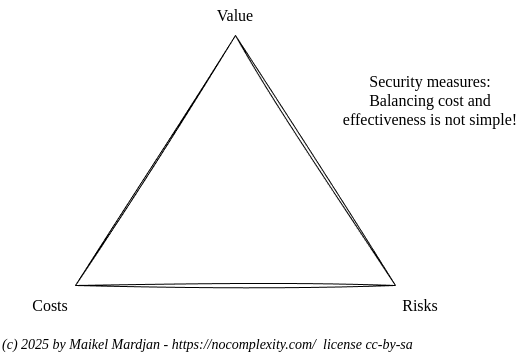
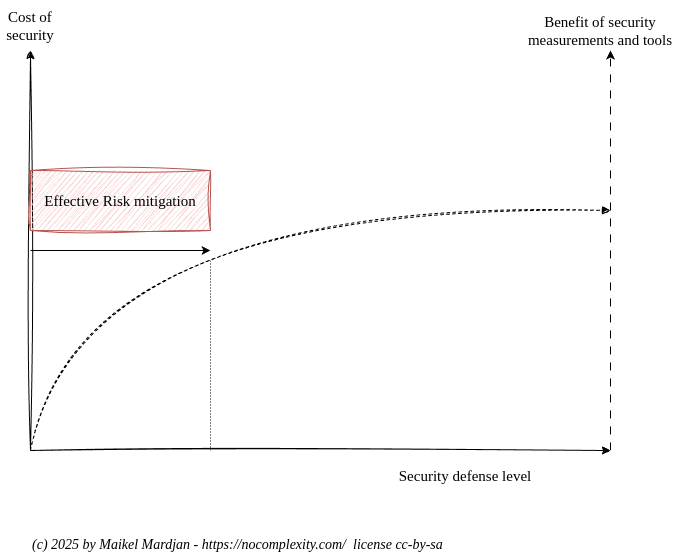
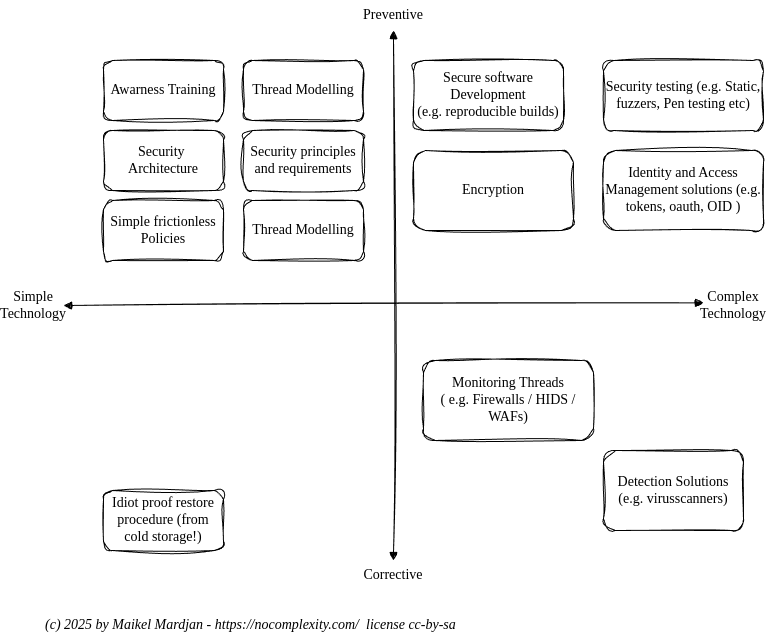
For many years, we have struggled to get security right. We,security experts and software developers, have been trained and influenced by commercial vendors. We use too many complex, expensive cyber security solutions that are costly to implement and maintain and lack transparency, as most enterprise cyber security solutions are not open source.
Next week, on Sunday 06-01 you are invited to join my talk on simplifying cyber security. Check the conference at t-dose.org and the schedule!
1 The State of SSL Stacks
TLS/SSL is complicated software. Multiple SSL stacks exist. This article gives a great overview with nice visuals. To master TLS/SLL you must continue learning, e.g. by reading articles like this.
(Link)
2 Why Bloat Is Still Software’s Biggest Vulnerability
‘Software is now (rightfully) considered so dangerous that we tell everyone not to run it themselves’ I advocate for simple secure software for many years. This article gives a great historical overview and tries to answer the question why software security is so bad.
(Link)
3 Secure Hardware Design
Understanding critical security problems in modern hardware and common limitations of existing security solutions is a must for security professionals. However most courses only touch the surface. This open course from MIT is great to improve your knowledge.
(Link)
4 Microsoft Security Sessions at Microsoft Build
A nice overview of all security session at the recent May 2025 Microsoft Build conference.
The URLs point to the presentation outline , including the option to watch the presentation or read and download the slides.
(link)
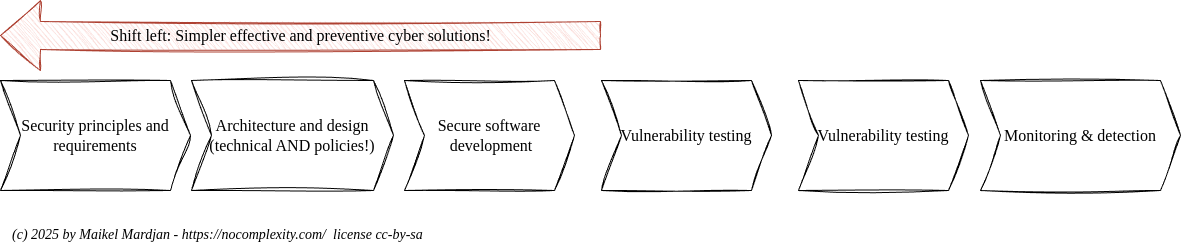
5 Why Security is Everyone’s Responsibility: A Call to Developers
Frequently I see blog articles with nonsense or an opinion that I strongly disagree with. This is such an example. The claim is ‘Vulnerabilities Start at the Code Level’. This is actually not true. Most vulnerabilities are due to having no security architecture, no threat model and maybe a mistake during coding. Coding mistakes are mostly detected during reviews or scans. Bad architectures and designs are never detected and are way more expensive to fix!
(link)
6 GDPR is cracking: Brussels rewrites its prized privacy law
Proposed changes to the GDPR will open a Pandora’s box of EU tech lobbying. Changing the GDPR threatens privacy again. Wondering who in the EU has time, energy, knowledge and resources to fight against this EU Trump department…
(link)
7 Oracle Database TNS vulnerability could leak data to further attacks
Unfortunate another example why patches are needed, but the damaged is already done.
This easily exploitable vulnerability allows an unauthenticated attacker with network access via Oracle Net to compromise RDBMS Listener.
(link)
8 New Privacy Principles for a more trustworthy web
Privacy is an essential part of the web. This document provides definitions for privacy and related concepts that are applicable worldwide as well as a set of privacy principles that should guide the development of the web as a trustworthy platform. See also the w3c blog post.
(link)
9 Go Cryptography Security Audit
Using FOSS building blocks can give benefits to reduce security threats. This great GOlang audit certainly helps building trust! Great work.
(Link)
Our partners:
The Open Security newsletter is an overview of cyber security news with a core focus on openness. Pointing out what went wrong after a cyber security breach is easy. Designing good and simple measurements is hard. So join the open Security Reference Architecture collaboration project to create better solutions together. Or become a partner to support this project. Use our RSS or ATOM feed to follow Open Security News.
]]>